Key Takeaways
- An information and cybersecurity framework isn’t a product, it’s a structured way of managing risk that stops you missing the gaps your tools can’t cover.
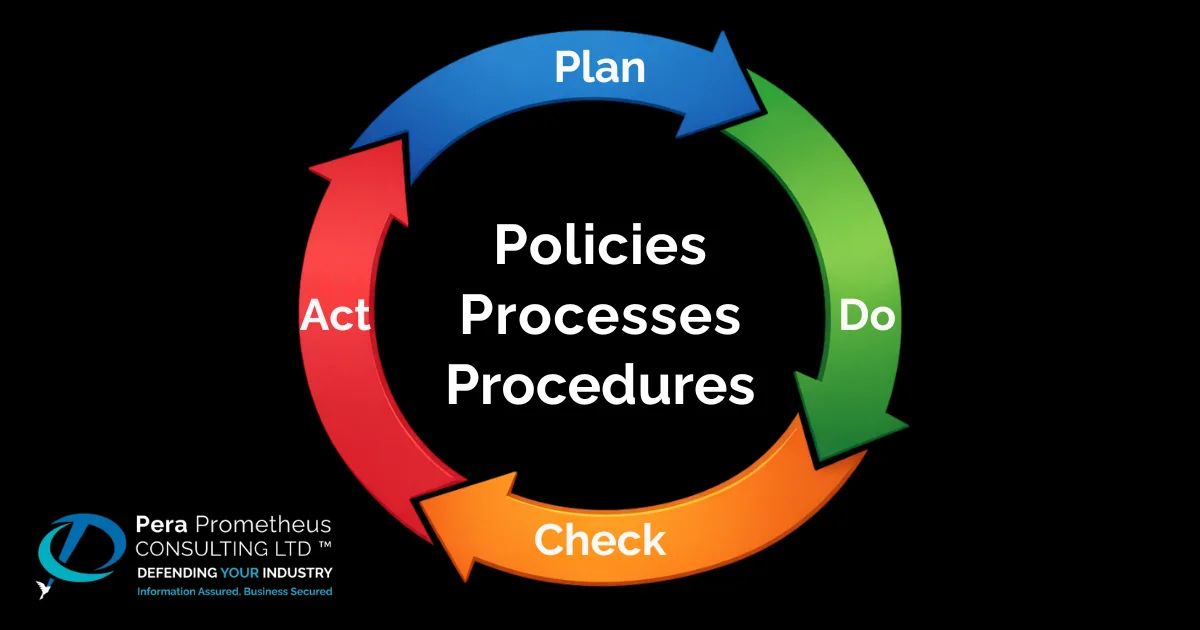
- Following a framework ensures that policies, processes, and procedures are repeatable, reproduceable, and reliable.
- The UK Government’s Cyber Security Breaches Survey 2025 found 43% of UK businesses experienced a breach or attack in the past year most through entirely preventable causes.
- For most SMEs in the Defence supply chain, Cyber Essentials is a baseline.
- You don’t need a dedicated security team to follow a framework, the NCSC’s free guidance is built specifically for small businesses.
- Choosing a framework that matches your current risk level matters more than immediately reaching for the most prestigious one.
Most businesses have some form of information and cybersecurity in place. Antivirus software, reasonably strong passwords, maybe a firewall. The problem is that having a handful of tools is not the same as having a plan. Without something to connect them, a framework, you end up with security that covers the obvious things and quietly ignores everything else. What is worse, this approach provides a false confidence that your business practices are secure when they most likely are not! A security framework doesn’t replace what you’ve already got. It gives it structure, and it shows you what’s missing. This blog explains what that looks like in practice, why it matters for UK SMEs, and where to start if you haven’t already.
What Is an Information and Cybersecurity Framework?
A security framework is not a piece of software. It’s not a product you buy or a checklist you tick off once a year and forget about. It’s a structured way of thinking about the risks your organisation faces, deciding what controls to put in place, and improving over time as things change. Think of it less like a burglar alarm and more like a building plan. It tells you what to construct, not just what to switch on.
Most small businesses approach security reactively. Something goes wrong, or a colleague recommends a tool, and it gets added to the pile. Over time you end up with antivirus here, a password manager there, maybe a bit of staff training after a near-miss. Each piece does something useful, but nothing connects them. Even more common is the use of 3rd Party Service Providers for SME IT systems which, in many cases, the SME assumes that the service provider is covering all security concerns – this often isn’t the case and you should not assume a service provider cares more about your business than you do.
The issue often is, nobody has sat down and asked: what are we actually trying to protect, and from what? A framework forces that conversation and once you’ve had it, the gaps tend to become obvious very quickly. Which matters, because those gaps are exactly where the problems tend to start. The UK National Cyber Security Centre (NCSC) has provided relevant information like NCSC — Guidance for Small and Medium-Sized Organisations and NCSC Small Business Guide.
Why Ad Hoc Security Leaves You Exposed
Here’s a stat worth sitting with. According to the UK Government’s Cyber Security Breaches Survey 2025, 43% of UK businesses experienced a cyber security breach or attack in the past year. The most common cause wasn’t a sophisticated hack or a state-sponsored attack. It was phishing, someone receiving a convincing email and clicking the wrong link. That’s the kind of attack a decent security awareness programme and a clear incident response process would significantly reduce.
The issue with ad hoc security isn’t usually the tools themselves. It’s everything around them. Who has access to what systems, and why? What actually happens in the first hour after a breach? How would you know if a staff member’s credentials had been quietly compromised weeks ago? Without a framework, these questions either don’t get asked, or they get answered inconsistently by different people at different times. Attackers know this. The gaps they exploit aren’t random. They follow predictable patterns, and they show up in businesses of every size that assume they were doing enough. So what does doing enough actually look like?
The Main Frameworks Worth Knowing
The good news is you don’t need to start from scratch. There are established frameworks designed specifically for organisations like yours, and the right one depends on where your business is now and where it’s heading. If you want a broader view of how frameworks sit alongside other compliance obligations, our Cybersecurity Compliance Guide covers the wider landscape. For most UK SMEs, though, it comes down to three options.
1. Cyber Essentials is the UK government’s baseline certification, backed by the National Cyber Security Centre. It focuses on five core controls: firewalls, secure configuration, access control, malware protection, and patch management. It’s practical, affordable, and built to be achievable without a large IT team. It’s also increasingly required, not just expected, by clients and prime contractors in the defence and public sectors.
Pera Prometheus is an approved Certification Body for both Cyber Essentials and Cyber Essentials Plus. We don’t just help you prepare, we carry out the assessment directly. If you’re wondering what the process actually involves, our Cyber Essentials FAQs are worth a read before you start.
2. The NCSC’s 10 Steps to Cyber Security is a broader framework for organisations ready to go further. It covers risk management, network security, identity and access control, incident response planning, and supply chain security, all in plain English, all free to access. It’s a natural progression once your Cyber Essentials foundations are in place, and it aligns well with what larger clients and government bodies expect to see as contracts grow in size and sensitivity.
3. IASME Cyber Assurance is a practical, UK focused standard designed to help SMEs demonstrate strong, proportionate cybersecurity governance. It sits above Cyber Essentials in terms of depth, covering areas like risk management, incident response, and supplychain security, but without the heavy resource burden of ISO 27001. For many businesses, it’s an ideal stepping stone: credible enough to reassure clients and primes, especially in defence and publicsector supply chains, while remaining achievable with sensible effort.
4. ISO 27001 is the international standard for information security management systems (ISMS). It demands considerably more resources than either of the above, but it carries real weight on larger contracts, particularly in international or high-value government work. If you’re not there yet, it doesn’t need to be your immediate focus. But it’s worth knowing it exists and roughly what the path towards it looks like, especially if you have ambitions to grow within the defence or public sector. You can learn more about ISO 27001 on our blog here.
Framework within Defence Supply Chain
If your business is already in the defence supply chain or you’re trying to get there, the question of which framework you need has a fairly direct answer. The MOD requires Cyber Essentials as a minimum for most supply chain contracts under DEFCON 658. It flows down the chain to sub-contractors too.
There’s also a newer development worth knowing about. The MOD and IASME have launched the Defence Cyber Certification (DCC) scheme — a four-level framework running from L0 to L3, intended to replace the old contract-by-contract self-assessment process with a single, organisation-wide certification. Cyber Essentials sits at the base of every level. The scheme is rolling out in phases and MOD have yet to formally commit to the scheme in the form of an Industry Security Notice. DCC can be expensive after Level 0 so if you want to understand what preparation looks like step by step, our guide to getting ready for DCC is a useful place to start.
Where to Start If You’re Not Sure
The most common question we hear isn’t “which framework should I use?” It’s “where do I even begin?” And the honest answer is simpler than you’d think. Start with the NCSC’s free Small Business Guide. It takes under an hour, it’s written for people without a security background, and it will show you fairly quickly where the obvious gaps are. Consider it your starting point before committing to any formal certification.
If your business handles any government or defence information, even at arm’s length, Cyber Essentials should be your first concrete target. And if you’re not yet sure what level of risk you’re actually carrying, that uncertainty is itself a signal worth acting on.
Ready to Take the Next Step?
Getting started with an information and cybersecurity framework is not as complicated as it first looks but it’s much harder to do well without the right guidance. At Pera Prometheus, we work with SMEs at exactly this stage. Get in touch and let’s talk through where you are.
Frequently Asked Questions
Q: What’s the difference between Cyber Essentials and ISO 27001?
A: Cyber Essentials focuses on the cyber environment entirely, covering five specific technical controls. In many cases it is the MOD’s minimum requirement for supply chain contracts. ISO 27001 is a comprehensive international standard for Information Security Management System (ISMS) that takes considerably more resources to implement but carries more weight on larger or international contracts as it focuses on all elements of security, not just the cyber environment. Most SMEs start with Cyber Essentials and build from there.
Q: Do I need a cyber security framework if I’m a small business?
A: It is very much advisable to have one. A single incident can have an outsized impact on a small organisation, and the NCSC’s free guidance is specifically designed for businesses without a dedicated IT function.
Q: How long does it take to implement Cyber Essentials?
A: For most small businesses with basic measures already in place, four to eight weeks is a realistic timeline including the assessment. As an approved IASME Certification Body, Pera Prometheus can guide you through the process and help close any gaps beforehand.
Q: Is a cyber security framework a legal requirement in the UK?
A: Not through a single piece of legislation but UK GDPR requires “appropriate technical and organisational measures” to protect personal data, which a framework directly supports. In the MOD supply chain, Cyber Essentials is a mandatory contractual requirement for the vast majority of contracts. It serves as the baseline for the Cyber Security Model (CSM), which is enforced through specific contract clauses.
Stay Safe, Stay Secure